Image-with-caption. Do not delete! This box/component contains JavaScript that is needed on this page. This message will not be visible when page is activated.
Let’s make this work.
To view this video, change your targeting/advertising cookie settings.
Is your city CyberSmart?
Let’s make this work.
To view this video, change your targeting/advertising cookie settings.
Are you ready for the Future of Health?
Let’s make this work.
To view this video, change your targeting/advertising cookie settings.
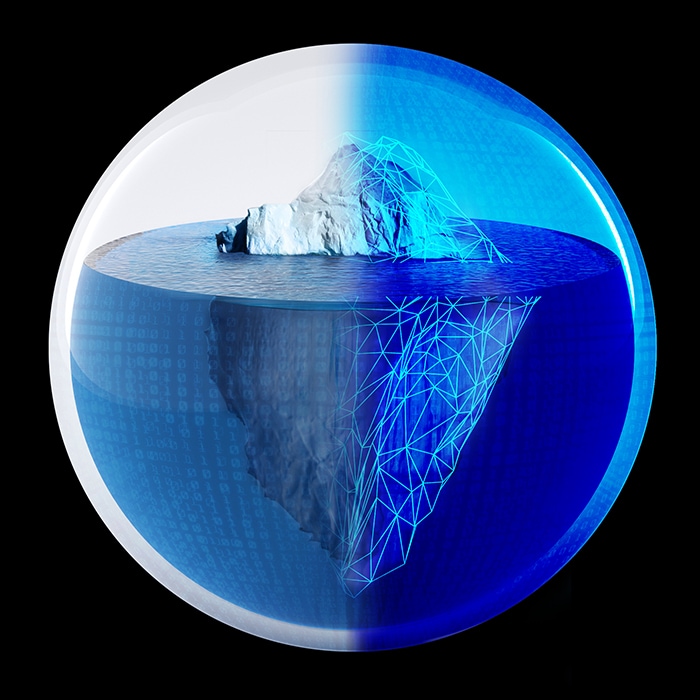
Cyber everywhere
Services
-
Security—reinventing how to go beyond risk to drive real results
Deloitte and Google Cloud are collaborating to provide end-to-end core security solutions to help protect your data, users, and applications.
-
Put threats at a disadvantage
Let our strategic and cyber risk management provide visibility and actionable intelligence that puts threats on defense—and your next opportunity in play.
-
Risk & Financial Advisory Services
We help organizations navigate business risks and opportunities—from strategic, reputation, and financial risks to operational, cyber, and regulatory risks.
-
Cyber Incident Response Services
See how Deloitte’s Cyber Incident Response Services can help your business prepare for, respond to, and rebound from cyber threats with speed and resilience.