States at risk: The cybersecurity imperative in uncertain times A joint biennial report (6th edition) from Deloitte and the National Association of State Chief Information Officers (NASCIO)
3 minute read
15 October 2020
The pandemic has highlighted public-sector cyber leaders’ resilience—but has also called attention to long-standing challenges facing state IT and cybersecurity.
Learn More
Download the full report
Read the 2018 survey
Learn about Deloitte’s services
Go straight to smart. Get the Deloitte Insights app
During 2020, chief information security officers (CISOs) have risen to the challenges brought on by the pandemic, working closely with state IT departments to balance cybersecurity risks and business continuity. With most employees unexpectedly working from home for an indefinite period, CISOs secured networks for remote work by enabling or expanding multifactor authentication, enhancing system monitoring to receive early detection and alerts, and reviewing readiness plans to address the possibility of unexpected cybersecurity incidents. CISOs’ actions helped most states maintain essential business functions and service to citizens, even in a time of tightly constrained cyber budgets.
This year’s study, based on responses from enterprise-level CISOs in 51 US states and territories, made clear state governments’ need for digital modernization and the essential role of cybersecurity. Survey results suggest that the CISO position has evolved into a mature and respected role, with the pandemic further highlighting its critical nature.
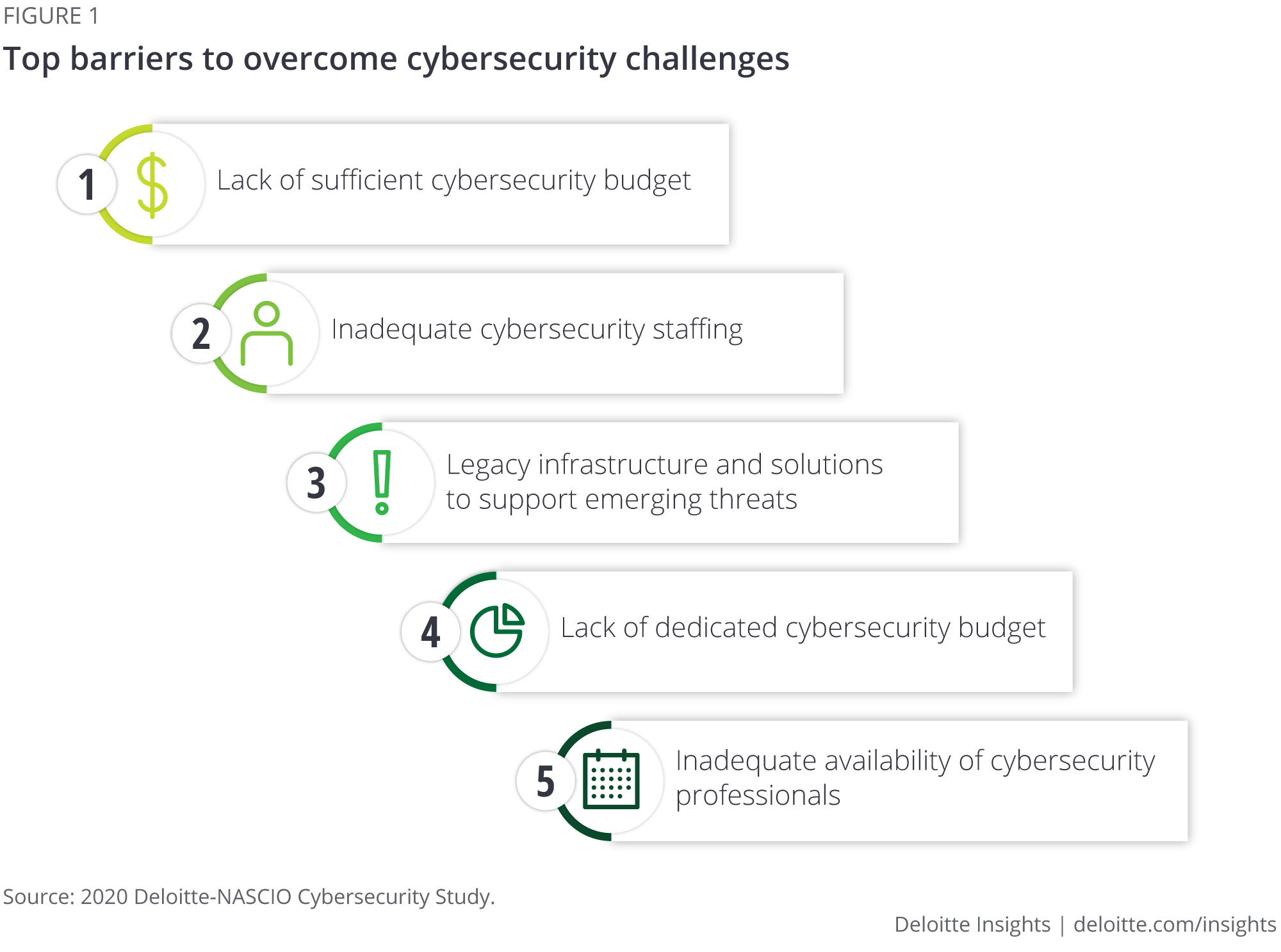
And yet CISOs struggle with the challenges of securing adequate budgets and talent, as well as coordinating a consistent security implementation across agencies. Our survey identified several key takeaways critical to further enhancing the CISO's status:
COVID-19 has challenged continuity and amplified gaps
One of the most notable challenges CISOs faced during the pandemic was the abrupt shift to remote work. According to the study:
- Before the pandemic, 52% of respondents said less than 5% of staff worked remotely.
- During the pandemic, 35 states have had more than half of employees working remotely; nine states have had more than 90% remote workers.
“The pandemic forced state governments to act quickly, not just in terms of public health and safety but also with regard to cybersecurity,” says Srini Subramanian, Deloitte & Touche LLP's state and local government advisory leader.
Connecting the cyber dots across state, local, and higher education
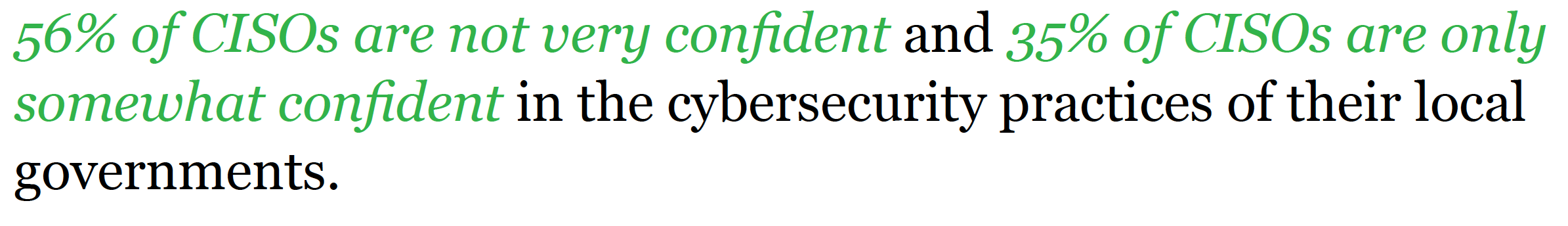
The pandemic has amplified state governments’ longstanding need for digital modernization, along with the essential role that cybersecurity needs to play in the discussion. Only 28% of states reported that they had collaborated extensively with local governments as part of a security program during the past year, with 65% reporting limited collaboration. By extending the CISO's influence through collaboration and partnerships, states can help provide cybersecurity services and guidance to often-overwhelmed local governments and public higher education entities.
Strength, consistency, and enforcement in numbers
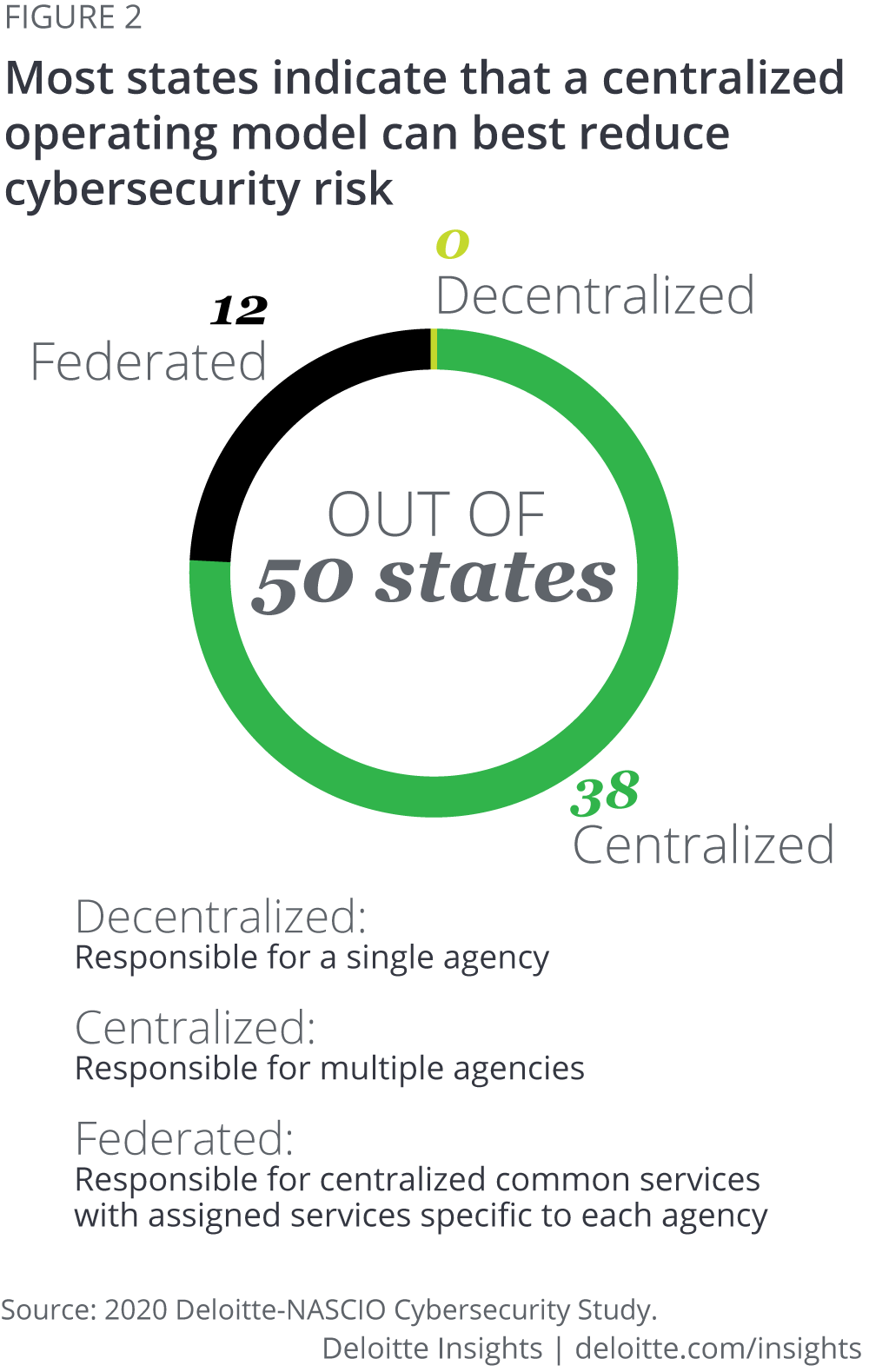
The study shows that 40% of the states continue to operate in a federated model, in which CISOs are responsible for enterprise policy with a mix of centralized shared services and agency-led services specific to each, and 10% operate in a decentralized model of cyber governance in which individual state agencies are on their own for cyber services and execution with only policy guidance from the CIO. To further their progression, state CISOs should transition to a centralized form of governance for the cybersecurity function, with the enterprise CISO responsible for cybersecurity for all state agencies while maintaining proximity to business initiatives at the agency/program level.
Progress on the 2018 Deloitte-NASCIO Cybersecurity Study bold plays
The 2020 study also reviews progress made toward the three “bold plays” identified in the 2018 Deloitte–NASCIO Cybersecurity Study1, covering funding, innovation, and collaboration.
The bold plays are strategic shifts that may take years for results to be visible, and our 2020 survey results show that while progress is being made, now is not a time to declare victory. In fact, it is critical to continue pressing forward on these bold plays.
More on technology in government & public services
-
5G in government Article4 years ago
-
Move faster, safer, and more privately with smart security Article4 years ago
-
COVID-19 and the virtualization of government Article5 years ago
-
The realist’s guide to quantum technology and national security Article5 years ago
-
AI readiness for government Article5 years ago
-
Cybersecurity in government Collection











