3D opportunity and cyber risk management has been saved

3D opportunity and cyber risk management Additive manufacturing secures the thread
23 August 2016
While cyber risk is pervasive, additive manufacturing (AM) is one area where it can be especially dangerous, due to AM’s reliance on digital files and connectivity, and the impact on multiple parties through the supply chain. An important part of developing a comprehensive cybersecurity approach is to examine relevant standards and regulations.
Introduction
Cyber threats are not new. In fact, it is difficult to find an industry sector, technology, or organization that is immune to cyber risks. Examples of particularly damaging cyber attacks have been heavily covered in the news, including attacks leveraging such tactics as worms, spear phishing, and hacking. One worm, Stuxnet, was used to infiltrate Iran’s nuclear enrichment program, taking over centrifuges, causing them to spin out of control and become damaged.1 Many other examples of cyber attacks exist and can lurk in connected objects or software, including consumer digital equipment, smartphones,2 and USB-connected devices such as e-cigarettes,3 thumb drives, digital picture frames, and USB chargers.4
Additive manufacturing (AM) is one area where cyber risk poses an especially significant danger. AM, also commonly known as 3D printing, alters the way in which physical products are designed and produced. Designs are created digitally, and, via connected printers and production lines, can theoretically be manufactured anywhere, at any time—by anyone with the means to do so.5
AM’s reliance on digital files and connectivity can also open the process up to entirely new types of cyber threats, from product malfunctions to intellectual property theft and brand risk.
The digitalization of physical products through AM may prove to be disruptive, opening up new opportunities to revolutionize the supply chain and create new parts and products that were previously impossible using traditional manufacturing. Indeed, the benefits and opportunities provided by AM are significant and have been explored in depth throughout Deloitte’s 3D Opportunity series.6 Manufacturers across sectors—from health care and automotive to aerospace and defense—are realizing AM’s many benefits in optimizing product designs, printing at or close to point of use, streamlining inventory management, and saving resources and costs throughout the product life cycle.7 Its use is expected to grow significantly, from $4.1 billion in 2014 to more than $21 billion globally by 2020.8
But AM’s reliance on digital files and connectivity can also open the process up to entirely new types of cyber threats, from product malfunctions to intellectual property theft and brand risk, along with other new threats conventional manufacturers may not face. For example, the data generated about an object during the AM design and production processes can be considerable, generating a strand of information that runs through the AM object’s lifespan known as the digital thread—and creating a trove of potentially vulnerable information.9
Developing a comprehensive AM cybersecurity approach is further complicated by the fact that cyber risk implications of AM affect multiple parties throughout the supply chain, from suppliers to owners, managers, and purchasers of AM systems, to distributors and purchasers of AM products. Cyber risk can impact each stage of the digital thread, from design and scan, to quality assurance and printing, to use in the field, and even disposal of the AM objects or printers.10 Indeed, AM’s existence at the intersection of the digital and physical worlds mean that, while companies seeking to apply AM must protect their digital assets, cyber risk extends to both the physical and logical objects associated with the entire process.
Organizations seeking to realize the benefits of AM can benefit from taking a proactive approach to addressing cyber risk. To help organizations that are exploring AM understand the broader impacts of cybersecurity in this environment and potential safeguards, this paper:
- Aims to explain how cyber risk affects AM along the paths of the AM framework
- Examines the characteristics that make AM unique with respect to cybersecurity
- Identifies various existing regulations and standards that can be applied to AM
- Outlines approaches to cybersecurity that organizations seeking to adopt and scale AM can incorporate
The additive manufacturing framework
AM’s roots go back nearly three decades. Its importance is derived from the ability to break existing performance trade-offs in two fundamental ways. First, AM reduces the capital required to achieve economies of scale. Second, it increases flexibility and reduces the capital required to achieve scope.11
Capital versus scale: Considerations of minimum efficient scale can shape supply chains. AM has the potential to reduce the capital required to reach minimum efficient scale for production, thus lowering the manufacturing barriers to entry for a given location.
Capital versus scope: Economies of scope influence how and what products can be made. The flexibility of AM facilitates an increase in the variety of products a unit of capital can produce, reducing the costs associated with production changeovers and customization and, thus, the overall amount of required capital.
Changing the capital versus scale relationship has the potential to impact how supply chains are configured, and changing the capital versus scope relationship has the potential to impact product designs. These impacts present companies with choices on how to deploy AM across their businesses.
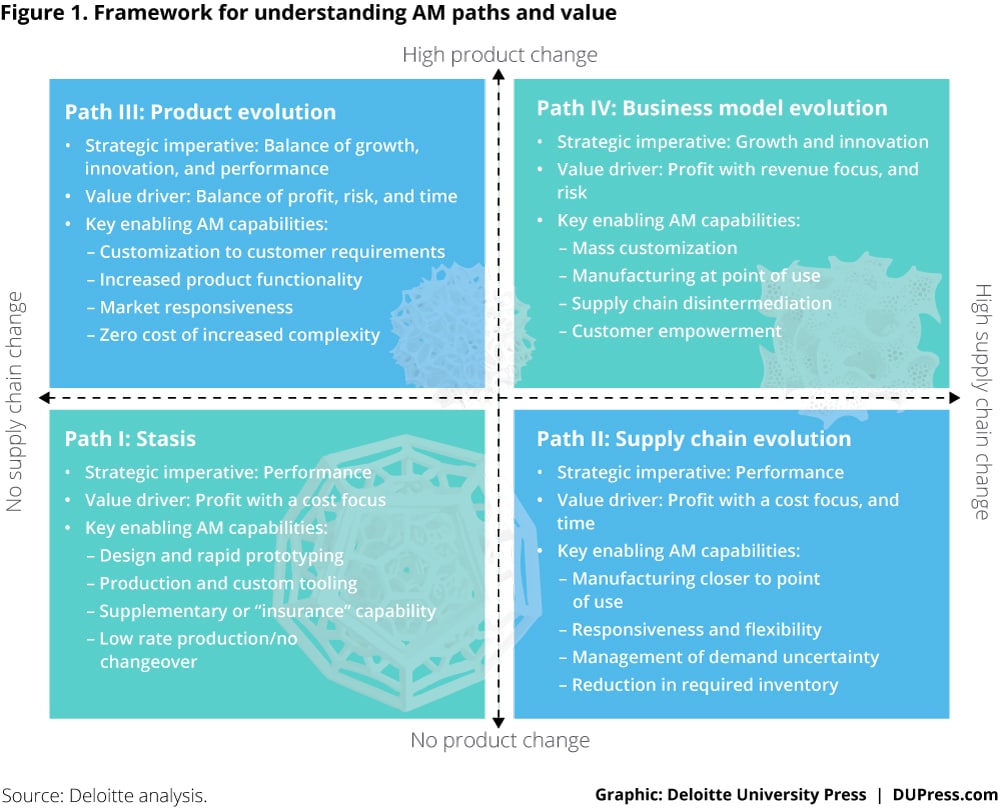
Companies pursuing AM capabilities choose between divergent paths (figure 1):
Path I: Companies do not seek radical alterations in either supply chains or products, but they may explore AM technologies to improve value delivery for current products within existing supply chains.
Path II: Companies take advantage of scale economics offered by AM as a potential enabler of supply chain transformation for the products they offer.
Path III: Companies take advantage of the scope economics offered by AM technologies to achieve new levels of performance or innovation in the products they offer.
Path IV: Companies alter both supply chains and products in pursuit of new business models.
Depending on their capabilities and how they intend to apply AM within their organization, companies may find themselves along different paths. However, cybersecurity concerns remain applicable no matter the path pursued; risks range from theft of intellectual property to loss of brand value, and even to malfunctioning of finished products in the latter paths. Once companies understand where they lie along the framework, they can begin to determine what they need to protect, consider the steps they can take to do so, and implement a rigorous cybersecurity strategy.
The special cyber risks for AM
Wherever data and information are transmitted, used, or accessed, companies must anticipate that someone, somewhere will try to exploit those data and information for personal gain or to inflict harm or damage. Understanding who executes cyber attacks and why they do so can help manufacturers in general—and additive manufacturers, in particular—anticipate possible threats.
Early on in the digital revolution, incidents of system breaches were not necessarily for malintent, but rather caused by people curious to see if and how they could gain access to systems.12 Many attacks have been focused on accessing what makes the organization competitive; in many cases, companies may be unaware that their systems have even been breached.13 Today, however, cyber attacks can and do cause real and sometimes significant damage to companies and individuals—and particularly to manufacturers. Cyber attacks can originate from individuals or organizations who are driven by a variety of reasons, including economic gain, the desire to cause damage to a specific company or companies, or as a means to disrupt society. In extreme cases, the objective may be to cause threat to life and safety. (See the sidebar “Applying the lessons of well-known cyber attacks to AM.”)
When it comes to manufacturing, chief threats can include theft of intellectual property by nation-states or competitors, especially those able to compromise insiders or business partners. Table 1 provides a conventional manufacturer’s view of six classes of cyber threat actors mapped alongside seven impact areas, illustrating where the actors are most likely to operate based on previous incidents.14 The information in this heat map can also apply to companies using AM, as many of the impacts and actors may remain the same.
Framing the cyber challenge for the AM life cycle
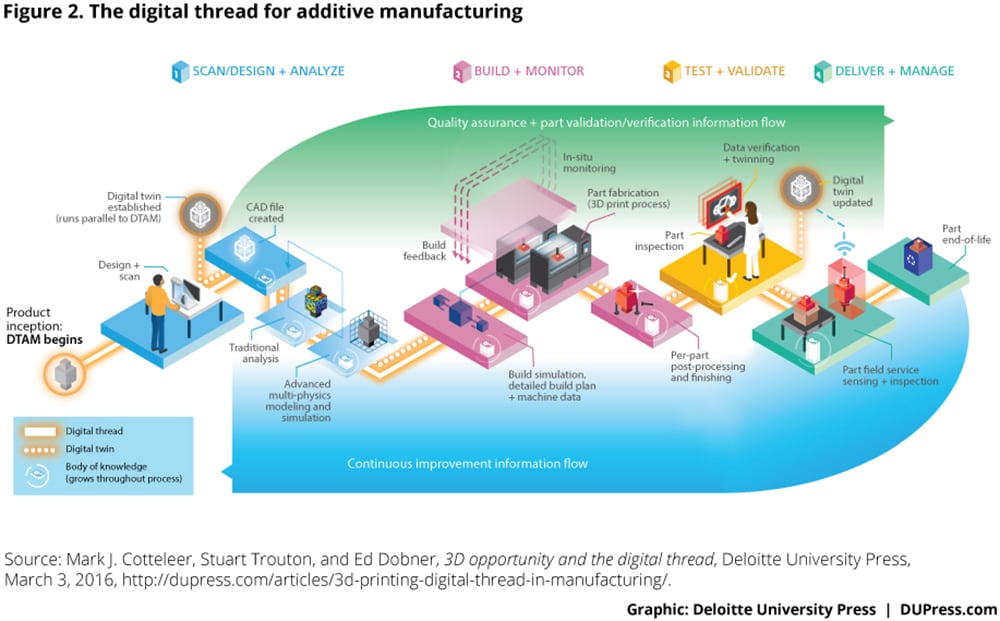
With the advent of connected and automated technologies such as AM, new threats—and new opportunities for access—are emerging. Figure 2 depicts the digital thread, the process by which information is created and communicated throughout the AM process, from design, build, and quality assurance monitoring, to testing, delivery, and distribution.15 At each step along this process are cyber risks related to intellectual property, software, firmware, network, IT, design, printers, productions, and the third-party supply chain. In this way, the digital thread can serve as a life cycle of sorts for examining the ways in which connected technologies interact throughout the manufacturing process, and the resulting threats that can arise.
The digital thread also illustrates the connectivity inherent in fully realized AM processes, and thus the unique cyber risks the process faces beyond those of conventional manufacturing. Indeed, as AM’s printers and systems benefit from becoming ever more connected and networked, cyber risks can affect AM-enabled production and machine functionality in a variety of ways. Table 2 matches some of these AM-specific cybersecurity concerns with some of the potential impacts described in table 1.
AM’s reliance on digital data files—and connectivity to transmit them—has numerous benefits for supply chain optimization. But it also means that once a file is stolen, hackers have access to the entire file in all of its intricacy, rather than simply to a physical object manufactured via conventional means that requires reverse engineering to create unauthorized or pirated copies. Whereas with conventional manufacturing, those looking to steal or copy a design would still need the means to produce it—knocking out the majority of would-be thieves—with AM, possession of the design file and a printer can make it far easier to produce the stolen object. This can pose risks related not only to health and safety but also to brand and liability should the devices fail or cause injury.17
Further, with access to a full design file, hackers could conceivably build in failure points in critical components without the designers’ knowledge, which would then be included in any object printed from that file. For example, the ACAD/Medre.A worm steals CAD files; another example, CryptoLocker Malware, infects a file and locks it, rendering it inaccessible to the user until she pays a ransom to unencrypt it.18 In other cases, toolpath files can be altered to impact placement of materials or layers during the build process, making a product unstable.
AM also possesses multiple other facets that make its cybersecurity concerns unique: a broad set of stakeholders, unique supply chain considerations, and a breadth of AM applications, leading to a complex web of regulations. We examine each below.
Applying the lessons of well-known cyber attacks to AM
Examining real-life cyber attacks in other connected, complex systems may illustrate some of the potential threats faced by AM-specific organizations or processes. These examples span sectors and illustrate the breadth of cyber risks.
Manufacturing: In one particular example of spear phishing—a tactic in which access to a network is obtained via email or other forms of communication—attackers infiltrated production networks of an IoT-enabled German steel mill and caused breakdowns of control components and entire installations. Ultimately, they caused an uncontrollable shutdown of a connected blast furnace and massive (although unspecified) damage.19
Automotive: Documented hacking techniques—including rewriting firmware on a critical chip in a connected car’s entertainment system—were used to give attackers wireless control of an automobile via the Internet. The hackers were able to control entertainment systems, windshield wipers/washers, transmissions, acceleration, and brakes.20
Retail: A major retailer endured a breach in which hackers gained access to customers’ personal data, finding a way into payment systems via the company’s remotely accessible HVAC system.21
Health care: Hackers broke into a connected, Bluetooth-enabled insulin pump to control insulin dosages, underlining the potential for harm to the patient.22
A broad set of AM stakeholders
AM can include a larger, more diverse group of stakeholders than conventional manufacturing, including owners, managers, and purchasers of AM systems, and suppliers of AM print materials. With a product life cycle extending beyond design and production, stakeholders can also comprise designers, vendors, purchasers, maintainers, and disposers of AM products, among others. This breadth can, in turn, translate to increased cyber risks. Some stakeholders may not have experience with cybersecurity issues, even if those issues, overall, are not new. This is particularly true for those who operate in makerspaces producing small-batch runs, and who may have limited experience with the cyber risks that accompany digital production. (See the sidebar “The maker movement and cyber risk.”)
As AM’s printers and systems benefit from becoming ever more connected and networked, cyber risks can affect AM-enabled production and machine functionality in a variety of ways.
Unique supply chain considerations
AM’s strong impact on the supply chain has been examined extensively in the 3D Opportunity series.23 In many ways, the supply chain for AM can consist of a design file, transmitted to the point of need for printing. This ability to print at or close to the point of need, on or close to the time of need, has tremendously positive implications for the supply chain in general as well as other implications for cybersecurity. To maintain the integrity of this largely digital supply chain, organizations must think beyond the file itself to consider all the other potential points of entry into the system and throughout the digital thread—something conventional manufacturers may not have to take into account. This can include tracking, tracing, and controlling distribution of certain materials, particularly those used to manufacture potentially dangerous products such as weapons; maintaining the integrity of design files; and controlling the distribution of design files to prevent counterfeiting. Some AM manufacturers have also considered tagging products with markers to indicate that products have been manufactured by design files, machines, and ingredients that have not been tampered with.24
The maker movement and cyber risk
AM is an important part of the “maker movement,” which is founded on the principle that making things is fundamental to the human condition and something everyone should do.25 AM democratizes manufacturing by radically reducing the costs of manufacturing and putting the power of “making” into the hands of many. For example, in the “makernurse” movement, nurses harness AM to solve problems and innovate. A hospital in Galveston, Texas, has opened a “medical maker space,” where nurses have used AM to customize materials for individual patients.26 Some medical professionals are also looking to reduce the costs and delivery time of simple, yet critical, supplies by using AM to make the supplies themselves.27 While the maker movement offers tremendous potential across a variety of industries, it introduces new forms of cybersecurity risk. Design files are typically unsecured, and quality control may also be an issue. While these risks are, in many ways, traditional to a manufacturing process, the operating context and participants’ skills and knowledge are radically different. This area is, perhaps, AM’s most underrated cybersecurity challenge.
A breadth of AM applications
Potential uses for AM span numerous industries, as well as both the public and private sector. Indeed, AM is currently an area of great interest for the US Department of Defense (DoD) and other federal entities as a way to address supply chain challenges associated with unpredictable inventory and expensive-to-produce parts in remote locations.28 However, cyber risk is a concern: A printer breach can render it unable to produce crucial parts; a design file that is tampered with to introduce flaws to a jet, a weapon, or its component parts can affect national security. In the private sector, AM can be used in the automotive,29 health care and medical devices,30aerospace,31 end-use product,32 and even food sectors.33 Design files can be illegally downloaded to print anything from IP-protected objects without obtaining permission, to dangerous or illegal objects such as weapons.
Terrorism, tampering, theft, and consumer safety are four areas of AM cyber risk for the public sector. While 3D printing of complex weapons is probably not a near-term threat, terrorists using distributed AM to manufacture smaller-scale weapons, such as guns, explosives, and ammunition, is of greater concern.34
Tampering is another area of concern. By subtly tampering with design files, hackers could introduce flaws into mass-produced items such as medications or medical devices that could be hard to detect, causing large-scale harm. Counterfeiting and theft are also big risk areas. In one example, cargo thieves used AM printing to make counterfeit copies of devices such as ISO 17712 high-security cargo seals, locks, and padlocks, in some cases in as little as 10 minutes.35 A 3D scanner created CAD technical specifications needed to produce near-perfect replicas, allowing thieves to hide signs of tampering and making it difficult to identify the location or time of the theft. In one example, thieves posted a CAD master file for replicating keys to open freight padlocks on a website approved by the Transportation Security Authority (TSA), allowing anyone to access the information.36
A complex web of regulations
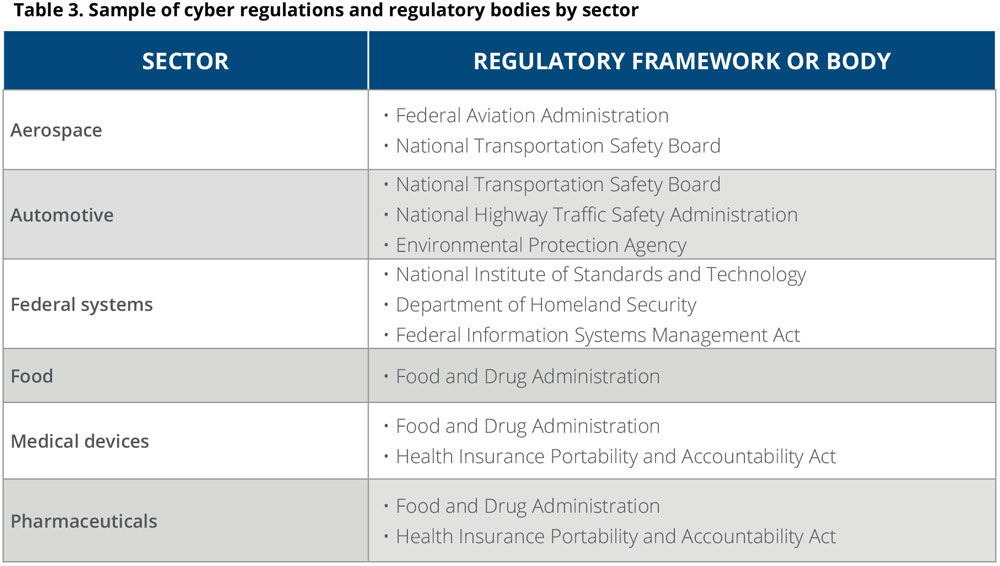
Due to the breadth of objects produced using AM across different industries, the technology is also beholden to a broad array of industry regulatory standards—as well as IT regulations that conventional manufacturers may not yet have to deal with, due to AM’s reliance on digital technologies. Thus, an organization’s cyber approach may need to be tailored to the specific regulation(s) needed to achieve compliance. For example, in the aerospace industry, AM use falls under Federal Aviation Administration (FAA) regulations. AM used in aviation or other transportation industries, including automotive, would have to comply with National Transportation Safety Board rules, but AM parts used in automotive exhaust systems would have to comply with Environmental Protection Agency rules. AM’s use in medical devices and pharmaceuticals can fall under Food and Drug Administration (FDA) and Health Insurance Portability and Accountability Act (HIPAA) rules. The FDA has been reviewing the use of AM in medical devices, and issued draft guidance around this in May 2016.37 To date, the FDA has approved more than 85 medical devices produced via AM.38
In this way, each AM application may require a different set of regulatory requirements with respect to cybersecurity (table 3). Regulatory guidelines can become further tangled as organizations leveraging AM navigate between the public and private sector—each of which come with their own attendant concerns.
Further complicating matters, AM printers can be considered IT systems, and their use by the federal government is regulated by Federal Government Information Security Act (FISMA) and policies supporting it, such as the National Institute of Standards and Technology’s Risk Management Framework (NIST RMF) and the associated Authorization to Operate (ATO) certification.39 More recently, the NIST Cybersecurity Framework (NIST CSF), which applies to critical infrastructure, is also being considered for application to federal programs. Federal cybersecurity regulations have been in place for nearly 20 years,40 yet federal agencies struggle with effective compliance.41 Indeed, the National Defense Industrial Association acknowledges that relatively less action has been taken to protect technical data.42 For their part, commercial vendors who may supply or contract with the government may be slow to react to cyber requirements. Adding to the challenge, some of these standards and rules date back to the 1980s, and much has changed technologically since their inception, particularly to AM and its attendant systems.43
Beyond the public sector, cyber risks associated with AM have implications within the health care space, where 3D printers are increasingly used to produce customized medical devices, drugs, implants, tissue, and even organs. Apart from obvious health-related concerns should security be compromised, machines that print medical devices or organs may also qualify as handling electronic protected health information and thus can be subject to the HIPAA security rule, adding additional layers of complexity. The ability to produce individualized products presents still more potential issues.44
The number of industries with their own governing bodies highlights that developing new cybersecurity standards and regulations for AM is a critical area for policy makers to explore. As with any emerging technology, policy gaps currently exist that may prevent stakeholders from implementing the most appropriate measures to protect AM data. Further, while the many cybersecurity frameworks, laws, and regulations listed before can help protect design files, the question remains how to ensure that they can work together, and whether or not they go far enough toward protecting AM systems and machinery. However, the development of new policies can take a long time—starting with identifying and testing leading practices, developing and testing standards, working with the US Congress to draft and pass new legislation where needed, and going through the rulemaking process, which can take several years45 —all before finally educating the public and enforcing the regulations.
With this in mind, AM stakeholders can get a head start by examining and applying existing standards, laws, and regulations. In particular, FISMA and NIST regulations can provide useful, actionable guidance, based on the risk management approach and supporting control infrastructure, along with other internationally accepted guidelines put forth by the International Organization for Standardization (ISO) and Institute of Electrical and Electronics Engineers.
Test once, satisfy many: Prioritizing the web of standards
As organizations seek to navigate the myriad regulatory bodies and regulations that impact AM cybersecurity, they can begin to consider how to address the many requirements potentially impacting any one organization and its supporting processes. Addressing every single regulatory framework individually can be neither effective nor efficient—nor, indeed, likely even possible. Shifting one’s mind-set, however, to look at the commonalities between the regulations can help make the process more feasible. In this way, organizations can take an overarching approach to which many regulations may align.
This strategy, “test once, satisfy many,” can enable organizations to consider the applicable regulations in the same vein to avoid duplicating efforts, particularly when used in concert with design approaches that incorporate security directly into the design of products. They can then create a comprehensive risk management framework to evaluate their regulatory environment to best address their specific cybersecurity footprint. Given the fact that AM processes include both digital and physical components, a combination of strategies focused on both IT systems and physical objects may provide the most comprehensive initial approach. Figure 3 depicts the creation and movement of digital information during the AM process via the digital thread and specifies the stages that involve consideration of IT systems, the physical object itself, or some combination of both.
With this in mind, the NIST RMF and NIST CSF may provide foundational frameworks with which to start this process of aligning controls to objectives and ultimately organization-specific execution.
Protecting IT systems: FISMA and NIST RMF
Given AM’s unique position that often transcends private and public sectors, organizations seeking to enact an AM cybersecurity plan may also need to consider the NIST RMF. The NIST RMF is a process developed for FISMA requirements, to allow organizations to assess IT security risks and make management decisions. FISMA requires that any new federal system complete an assessment and authorization review of the cybersecurity requirements of the NIST RMF before initial deployment and obtain ATO certification signed by a designated agency official.46 Although the NIST RMF was designed for federal government agencies, any organization may adopt it. Since FISMA also requires the same cybersecurity standards to apply to any IT system connected with a federal system, any organization working for or with the federal government can benefit from understanding the NIST RMF.
The NIST RMF defines a series of controls, grouped within control families or areas in which organizations must consider the security and privacy concerns within the systems. An organization can change the security categorization levels to which each control applies, rather than automatically accepting the NIST recommendations. Organizations can also add controls of their own to customize security to their needs. The NIST RMF can perhaps be most relevant during the scan/design and analyze, and build and monitor phases; during quality assurance; and potentially throughout the digital twin.
Beyond federal regulatory frameworks, organizations may also want to consider other global security standards such as ISACA’s Control Objectives for Information and Related Technologies (COBIT), ISO/IEC 27000, and ITIL, as well as cybersecurity standards from the European Telecommunications Standards Institute. The ISO 27000 and COBIT standards are already embedded as informative references within the NIST CSF, so application of the NIST CSF to an organization’s program can leverage existing work done with those standards.
Protecting the physical object: NIST CSF
Given AM’s unique position at the cross-section of physical object and digital thread, organizations seeking to enact an AM cybersecurity plan may also need to consider the NIST CSF in addition to the IT systems angle.48 The NIST CSF is rooted in a 2013 executive order focused on “improving critical infrastructure cybersecurity,”49 and is perhaps uniquely suited to AM cyber risk needs because it was developed jointly by the public and private sectors, across which many AM systems span. The NIST CSF is voluntary and allows organizations to take a broad, high-level view of their cyber risk program, incorporating existing standards and controls that are already in place, such as ISO 27000. In contrast, the NIST RMF is used to specify detailed controls that should be implemented at the system level. The NIST CSF was published in February 2014, along with a roadmap for additional aspects to be considered.50 NIST continues to maintain the CSF and periodically engages with the private sector through workshops to share implementation lessons learned. In addition, the Department of Homeland Security’s Critical Infrastructure Cyber Community C³ Voluntary Program “supports owners and operators of critical infrastructure, academia, federal government, state, local, tribal, and territorial governments, and business in their use of the National Institute of Standards and Technology’s Cybersecurity Framework.”51
The NIST CSF could potentially gain relevance in the latter phases of the AM process: quality assurance and in situ monitoring of the build process during the build and monitor phase, as well as during testing, validation, delivery, and management of the physical part.
Taking steps toward AM cybersecurity
As organizations seek to protect their AM systems and make sense of the vast array of guidelines and regulations that may impact their business, the path can seem daunting. Below are several steps manufacturers can take as they work to establish a robust AM cybersecurity strategy.
AM-specific applications of risk assessments can include examining the entirety of the digital thread, from scan/design to build and monitor, from test and validate to deliver and manage.
Conduct a thorough risk assessment
One of the first steps any organization can take is to conduct a security risk assessment. By doing so, it can pinpoint the risks most pertinent to its particular AM scenario, as well as any additional threats that might come into play as it explores other AM applications. This approach can, in turn, enable the organization to focus initial cybersecurity efforts on the highest-risk areas, and identify and prioritize the various points of vulnerability throughout the digital thread or digital supply network. AM-specific applications of risk assessments can include examining the entirety of the digital thread, from scan/design to build and monitor, from test and validate to deliver and manage.
Adopt a “test once, satisfy many” approach, at least in the short term
As organizations await standards more specific to AM, they can address the wide-ranging web of regulations currently in place by adopting NIST CSF and RMF approaches discussed in the previous section to address some of the more immediate challenges within the digital thread.
Protect the design from the start
The AM process—and the flow of digital information—begins at the scan/design phase, when the object is either designed using computer modeling or scanned via 3D scanning.52 During this stage, the design is vulnerable to outright theft, locking of the file to prevent its use, or corruption via introduction of malicious flaws.53 The current de facto standard file format for AM design files, .STL, is a plain text file.54 Currently, .STL has few provisions for supporting confidentiality (such as by allowing for encryption), integrity (such as by supporting digital signatures and checksums), authorization (such as by including license keys), or traceability to the original designers (such as by supporting digital signatures and public key infrastructure).55 However, standards are starting to emerge for encryption. Currently, most .STL design files are transferred to AM machines via USB drives that may or may not be encrypted. This is changing, however; organizations are developing encryption techniques to protect .STL files. Adopting an approach to protecting files from theft or tampering is an important part of an AM cybersecurity strategy.
Leading practices are emerging in the area of tracking and tracing, including the use of RFID tags to track AM-produced products throughout the supply chain. Another promising development is the use of chemicals to apply unique identifiers to AM products.
Build protection into the print process
Manufacturers can look to emerging standards to protect their AM processes during the build process. Leading practices are emerging in the area of tracking and tracing, including the use of RFID tags to track AM-produced products throughout the supply chain.56 Another promising development is the use of chemicals to apply unique identifiers to AM products; in one case, chemical tags were added to a composite during the jetting process.57 While the costs and business processes associated with using these emerging solutions need to be examined, they may show promise in terms of securing products throughout the supply chain and reducing the likelihood of tampering, theft, and counterfeiting. Further, a robust quality assurance methodology can help organizations detect toolpath alterations or other misplacement of materials, among other structural adulterations.58
Beyond adding traceable materials during the build process or monitoring quality assurance, organizations can consider putting measures in place to protect the machines themselves. AM printers do not typically limit and control who uses them, or what objects are printed. Until AM printer and file standards are developed to address those concerns, organizations using AM printers can adopt change management/control workflows for printers and objects, including reviews, and authorized approvals. This allows organizations to have some level of confidence that any objects printed comply with IP rights, license agreements, and other security concerns, as well as that viruses will not be introduced to impact the printer’s function, as with Stuxnet’s impact on centrifuges. AM organizations can model their approach to these workflows on those already in use for other technologies, such as change control boards or configuration control boards commonly used in software management. To ensure an AM printer prints only approved objects, the printer may be isolated on the network, with controls in place to make sure only approved designers can submit files directly to the printer.
While changes to the technology itself may be impractical, if not impossible, changes to AM-related policies and procedures can help address many of these issues. There is precedent for these sorts of policy changes. For example, the entertainment industry was ultimately able to limit file-sharing technology largely by ensuring that incentives and advantages for compliance outweighed the difficulties.59 While those engaged in AM may not be able to force all printers and machinery to comply with proposed procedures, they can emulate the entertainment industry by providing powerful incentives to smooth compliance.
Pick your battles
Simply put, addressing every single challenge may not be feasible; companies using AM must pick and choose their battles. For example, stopping every maker from printing copyrighted toys may not be possible, nor worth the effort. However, for producing particularly critical components for health care, automotive, or federal applications, more stringent approaches to securing AM machines, designs, and products are advisable. Organizations can, however, take a page from their approach to securing conventional manufacturing systems as they address concerns related to AM. For example, regulators such as the FAA may be able to require that AM printers and products used in their industries meet new regulations in the same way they ensure conventionally manufactured products meet current regulations.
Remember the most vulnerable asset: People
The breadth of stakeholders involved in AM—from owners, managers, purchasers of AM systems, and printing facilities in different locations, to materials suppliers and other vendors—can contribute to a host of potential cybersecurity threats and vulnerabilities. Some individuals may be new participants in the manufacturing process and may not understand the full implications of what they are doing and the security issues involved. Others, such as suppliers or printing facilities, may be using different systems or employ varying levels of security. Indeed, at a symposium held by NIST in February 2015, experts observed that “the biggest challenge to building cybersecurity . . . is culture.”60
By conducting a stakeholder analysis, manufacturers can identify parties involved in their AM efforts, both throughout the digital thread and the supply chain. Manufacturers can then work to educate these stakeholders about the importance of cybersecurity, and emphasize the risks and the importance of vigilance. Basic awareness building and ongoing education can go a long way toward mitigating security risks, encouraging individuals to exercise care and take precautions, and recognize the importance of using security systems. At the same time, it is important to note that when conducting awareness and education, tone matters. The intent should be to encourage AM participants to use leading security practices, not to discourage use of AM technology or appropriate security practices.
Conclusion
AM offers great promise in terms of democratizing and distributing manufacturing, reducing waste, and enabling rapid production of new and specialty products. Some of the possibilities, such as printing organs for those in need, are truly astounding. The use of AM is likely only going to grow in importance as its potential benefits for mass customization in health care; design innovation in automotive, health care, aerospace, and defense; and supply chain impacts in all sectors continue to be realized. Therefore, proactively addressing cyber risk is critical.
Indeed, the very nature of this new technology, with its focus on value in information rather than end product, leaves it open to significant security risks, ranging from securing design files to tracking and tracing authenticity of products made. There is much work to be done in terms of identifying comprehensive and sustainable AM cyber practices and promulgating them through standards and, where appropriate, additional regulation. Immediate steps such as conducting security risk assessment, developing mitigation plans, encrypting design files, protecting printers, and educating stakeholders can go a long way toward understanding and addressing AM cybersecurity concerns now. Those using AM need to monitor the development of new standards and solutions closely, and government and trade groups need to work diligently to identify concerns and develop and promote the use of leading standards to address these concerns.
Deloitte Consulting LLP’s Supply Chain and Manufacturing Operations practice helps companies understand and address opportunities to apply advanced manufacturing technologies to impact their businesses’ performance, innovation, and growth. Our insights into additive manufacturing allow us to help organizations reassess their people, process, technology, and innovation strategies in light of this emerging set of technologies. Contact the authors for more information, or read more about our alliance with 3D Systems and our 3D Printing Discovery Center on www.deloitte.com.