Decoding the FedRamp authorization process for cloud providers has been saved

Perspectives
Decoding the FedRamp authorization process for cloud providers
Answers and assistance to accelerate the authorization timeline
The Federal Risk and Authorization Management Program (FedRAMP) authorization is a recognized security milestone. But reaching the destination demands awareness and preparation. The FedRAMP cloud service providers have many questions regarding the process. We are here to answer those queries and assist them to strategize better.

What is FedRAMP?
Spurred by the U.S. Government’s Cloud First policy, the FedRAMP is a security assessment and authorization process created to provide a consistent and efficient mechanism for applying security and measuring risk in cloud resources used by federal agencies. FedRAMP authorizations are required for multi-tenant clouds that store federal agency data or metadata; they are needed for many U.S. Government cloud contracts.
How does it work?
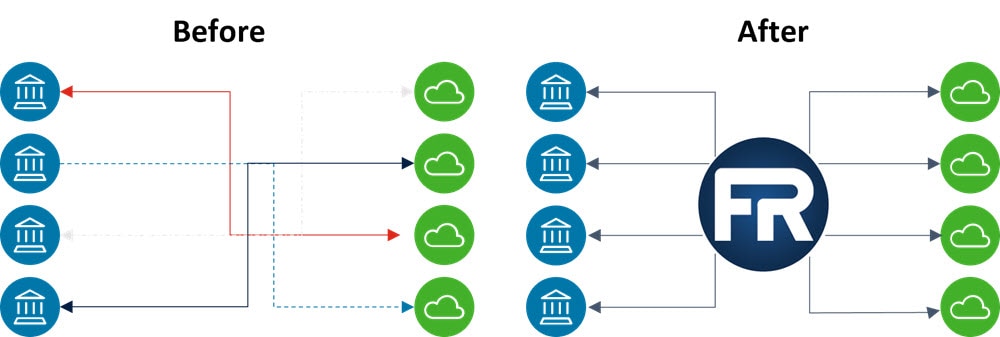
Despite recently becoming a law, FedRAMP does not operate on its own. It is a program that layers on top of the Risk Management Framework (RMF) and Authorization to Operate (ATO) processes employed by U.S. Government agencies when evaluating whether to use software and services. By issuing cloud-specific guidance and acting as a middleman, FedRAMP makes ATOs more consistent, trustworthy, and reusable across each agency. This means that when your organization is providing a multi-tenant cloud service to the U.S. Federal Government, you will be seeking two authorizations:
- An agency ATO, coming from your sponsoring agency (or a provisional ATO), will allow you to do business with your contracting agency
- A FedRAMP authorization, coming from the FedRAMP Program Management Office (PMO), will publicly acknowledge your service as a FedRAMP-authorized cloud service offering (CSO) and allow prospective U.S. Government clients to perform a security review of your system.

What are the different options?
The FedRAMP process is tailored to your offering as a Cloud Service Provider (CSP). Specific requirements vary based on the type of data stored in your system and how many agencies want to use it. For instance, three different FedRAMP impact levels are available to CSPs, depending on the sensitivity of the data they store. Also, CSPs may move through the FedRAMP process via agency sponsorship or the Joint Authorization Board (JAB).
- Develop business case (JAB only)
- Get prioritized by the JAB or establish agency sponsorship
- Define authorization boundary
- Create FedRAMP environment
- Create SSP and supporting documentationReadiness Assessment Report (JAB requirement, optional for Agency)
- Full security assessment
- Review and authorization by JAB or Agency sponsor
- Continuous monitoring
During and after your authorized Third-Party Assessment Organization (3PAO) assessment, you will be responsible for “Continuous Monitoring” or “ConMon” requirements for the duration of your security authorization. ConMon requirements are both operational and reporting-focused, and they help your sponsoring agency understand the ongoing security health of your organization.
Get in touch
Matt Bogusch |
Scott Maker |
Joe Bartos |
Recommendations
Cloud computing risks and the controls that weather the storm
Service providers can win customer trust with coveted certifications
Cybersecurity risk management examination
Staying one step ahead


